Don’t Take the Bait! Gone Phishing.
March 12, 2018
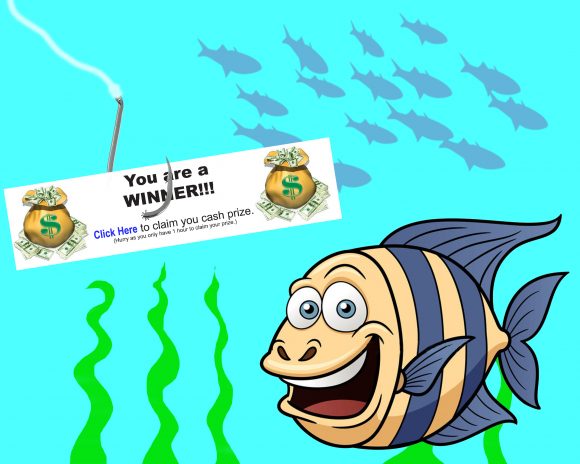
With Phishing, just like fishing, there is a lure, a line and a bucket. Of course, all of this is virtual.
Here is how it works.
The Lure:
The “Lure” is the part of the phishing scheme that you see. You receive an email that, at a glance, looks safe. Then you see a link that says, “Click here to keep your account active”, and your first reaction is to click the link. (in the same manner a fish would gulp that bait on a hook)
The “Fishing Line” is the part you rarely see.The fishing line pulls you somewhere you do not want to go. If you “took the bait”, the “Fishing Line” is a web address behind the hyperlink (the Lure), you clicked, which takes you to a website different than the advertised destination.
The Bucket:
Nobody wants to be in the “Bucket”. Even though you are not physically in a bucket, your online information is. The site you arrived at can display a log in prompt for your email/username and password. Or ask you to download something (usually in an urgent or threatening tone). Giving away your credentials could allow an attacker to gain access to all your Personal Data, such as Social Security Number, banking account, personal email, personal social networking accounts. And worse, it would grant them access to the Chapman Network, despite all the measures we take.
The End:
We know it can be difficult spotting a phish, and we want you to know that our Information Security team is ready to help. If you are interested in further training on spotting a phish, please register for one of our free “Online Security and Awareness” sessions. These on-line video tutorials offer tips on how to spot a phish and are completely self-paced. Simply email infosec@chapman.edu before the 20th of each month and we will register you for the interactive training.